Technology
We believe in security models backed
by mathematics
Here below is the scope of modern cryptographic academic fields we dive into and contribute to.
Access Control
Resource
To implement the Covercrypt algorithm: check out Cosmian GitHub repository here for more information.
Our approach
Our team has developed a more efficient multi-user encryption solution, named Covercrypt. Covercrypt provides access rights to users with respect to an access policy expressed as the union of users’ rights.
This construction is inspired by the Subset Cover framework proposed by D. Naor, M. Naor, and J. Lotspiech, which enables to broadcast of encrypted information to a group of users that dynamically evolves.
Covercrypt has the same functionalities of key-policy Attribute-Based Encryption but with a simpler approach and a more efficient performance.
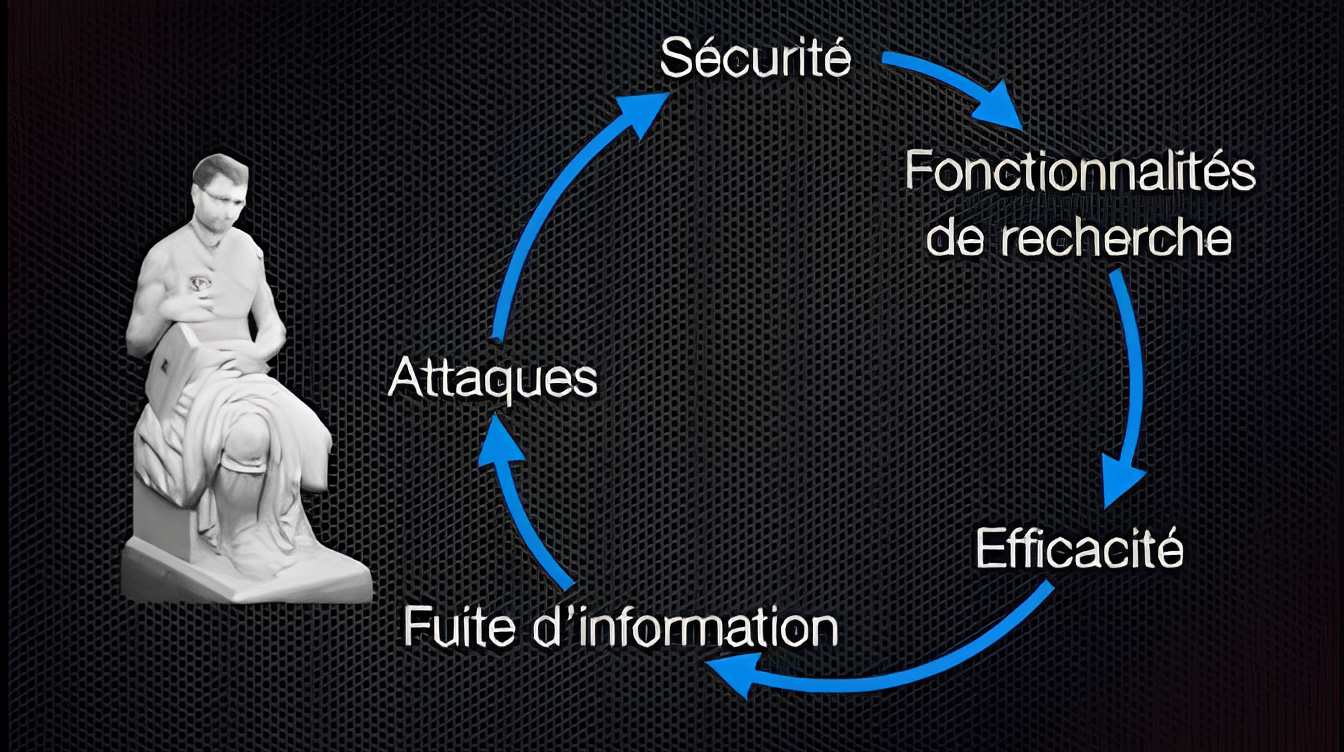
Searchable Encryption
Resource
Find more details in our technical documentation here.
Our approach
Searchable Encryption is a cryptographic protocol designed to securely make search queries on an untrusted cloud server. With encrypted indexes, large databases can securely be outsourced without compromising usability. After a search request, the cloud server can answer the list of all the entries matching the requested keyword without knowing either the keyword or the entries as everything is encrypted.
To provide our own version of this protocol, our team of researchers and cryptographers at Cosmian have developed Findex.
Findex is a Searchable Encryption library that allows the building of encrypted indexes that can be efficiently searched using encrypted queries and responses.
Academic papers
Read a critically acclaimed thesis, which won the GDR security prize in 2019, about Searchable Encryption.
More academics papers on that topic:
Secure Enclave
Resource
More information on Intel® SGX & Gramine SGX
Our approach
At Cosmian, we rely on Intel® SGX and Gramine-SGX, a lightweight guest OS designed to run a single Linux application with minimal host requirements. It is the foundation of Microservice Encryption which allows our users to expose a Python confidential web microservice in the cloud.
Computations over encrypted data using Fully Homomorphic Encryption
The results of these computations are also encrypted and only a user knowing the secret key is able to decrypt the result of the computation.
Our approach
A Heatmap is a graphical representation of the distribution of points. It is very useful to represent habits, buying or energy consumption for example.
With the collaboration of researchers at Leuven, we have proposed two methods for fast computation of Heatmaps over encrypted data using fully homomorphic encryption.
We are also interested in providing proof of correct homomorphic computations in interactive protocols between two users by reducing the amount of communication between the two parties compared to existing solutions. Such work finds applications to prove correct FHE computations in the context of private information retrieval or private set intersection computation with the help of homomorphic encryption.
Academic papers
The result of some of the team’s work on this topic can be find in the research paper MyOPE: Malicious securitY for Oblivious Polynomial Evaluation, (by Malika Izabachène, Anca Nitulescu, Paola de Perthuis and David Pointcheval), which was published and presented at SCN in September 2022.
Read the full version here.
Resources
The source code is public and can be found here
The two methods have been described in the paper Homomorphically counting elements with the same property, published at PoPets in July 2022,
Got a few minutes to spare?
Computations over encrypted data : Providing Calculation Results over Private Data
Enabling someone to compute calculation results over private data is necessary in many data analysis use-cases where it is sensitive and not owned by the analyser.
Functional Encryption provides primitives to disclose the result of a computation on private and encrypted data without the input data itself, and can be made non-interactive (which is not the case in Multi-Party Computation constructions), and restricted to jointly established functions (for example, a summation), to prevent the use of undesirable calculations.
Our approach
One of our cryptographer worked on a research paper which gives an interesting tool for many contexts in similarity or diagnoses calculations with private data from two independent parties, in the line of functional encryption.
More specifically, in graphs of banking transactions between private accounts spread across several banks, similarity measures between private graph nodes belonging to separate financial entities can help in the detection of money-laundering networks relying on banks not sharing their pattern observations, while keeping exclusive information encrypted so that it is never disclosed. (1)
We also wrote an implementation of Decentralized Multi-Client Functional Encryption (DMCFE) for inner-products; in this case, in an other fashion as in [PP22], the data is decentralized and there are no diagonal quadratic terms in the function, but only inner-products between the vector of the decryption key and the encrypted data.
One typical application would be for an entity to collect the sum of users’ private data, for instance for mean calculations.
Academic papers
Read more information on the research paper “Two-Client Inner-Product Functional Encryption, with an Application to Money-Laundering Detection“, (by Paola de Perthuis and David Pointcheval) published at CCS in November 2022.
Resources
Find more details on our implementation proposition in our GitHub.
Computations over encrypted data : Calculations on Graph-Structured Data
Graphs are structures represented as nodes linked with oriented or non-oriented (weighted) edges. Nodes can hold individual values and characteristics to describe them (such as labels, vectors of values).
Our approach
Our team has work on The CRYPTO4GRAPH-AI ANR project, in collaboration with the INRIA, Eccenca, and the Fraunhofer FIT. It aims at developing cryptographic solutions for graph-structures data.
One of the first results for this project is in functional encryption (see the corresponding section for more information), with [PP22], which has noticeable applications in graphs of bank accounts and their transactions.
Academic papers
Read the full version of the paper “Two-Client Inner-Product Functional Encryption, with an Application to Money-Laundering Detection”.
We proudly work with world-renown academic
and technology partners
We’re constantly in search of world-class partners